How To Fix Error : sun.security.validator.ValidatorException: PKIX path building failed:
sun.security.provider.certpath.SunCertPathBuilderException: unable to find valid certification path to requested target
You could get the error “PKIX path building failed” validation error when working on a client that works with an SSL enabled server running in https protocol. This article focuses on detecting the root cause of the error and on how to fix the issue.
There are other similar issues related the SSL certificates. One of the common situation is the missing certificate in trust store. In that case you may see the following error message.
Caused by: java.security.cert.CertificateException: No name matching localhost found at sun.security.util.HostnameChecker.matchDNS(HostnameChecker.java:210) at sun.security.util.HostnameChecker.match(HostnameChecker.java:77)
See the following article to read more about the above error and its solution.
Table of Contents
The first part of the error, “javax.net.ssl.SSLHandshakeException: sun.security.validator.ValidatorException: PKIX path building failed: “, indicates the type of error and the second part of the error message “sun.security.provider.certpath.SunCertPathBuilderException: unable to find valid certification path to requested target” gives an indication on what exactly went wrong.
Before diving into the cause and solution let us get some general knowledge 🙂

What is PKIX?
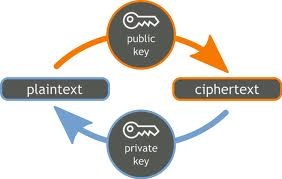
PKIX is Public-Key Infrastructure X.509. PKIX is public key infrastructure standards based on X.509 protocol. X.509 is an ITU-T cryptography standard for a public key infrastructure (PKI) and Privilege Management Infrastructure (PMI). Read references for more details on The PKIX (Public-Key Infrastructure X.509) Working Group (PKIX-WG).
PKIX path building failed : sun.security.validator.ValidatorException
This error is one of the many SSL related errors you may experience when you start developing applications those communicates securely. This happens during one of the SSL Handshake phase. This exception is of type javax.net.ssl.SSLHandshakeException, which indicates that the client and server could not negotiate the desired level of security. The connection is no longer usable.
The complete exception message is below:
javax.net.ssl.SSLHandshakeException: sun.security.validator.ValidatorException: PKIX path building failed: sun.security.provider.certpath.SunCertPathBuilderException: unable to find valid certification path to requested target
How to Detect PKIX Path Building Failed Error?
Even though this is a common exception while connecting a service over HTTPS, identifying the exact problem without proper debugging configuration is difficult. Unless you enable the SSL handshake debug mode (Java VM parameter -Djavax.net.debug=ssl:handshake) you will not be able to identify the root cause. Without SSL debug enabled you most likely will see the following error.
javax.net.ssl.SSLPeerUnverifiedException: peer not authenticated at com.sun.net.ssl.internal.ssl.SSLSessionImpl.getPeerCertificates(SSLSessionImpl.java:352) at org.apache.http.conn.ssl.AbstractVerifier.verify(AbstractVerifier.java:128) at org.apache.http.conn.ssl.SSLSocketFactory.connectSocket(SSLSocketFactory.java:572)
The above message is more generic and in most cases will not give you the root cause of the issue. Once you enable SSL handshake debug mode you will see the following exception trace:
http-localhost/127.0.0.1:8443-1, SEND TLSv1 ALERT: fatal, description = certificate_unknown http-localhost/127.0.0.1:8443-1, WRITE: TLSv1 Alert, length = 2 http-localhost/127.0.0.1:8443-1, called closeSocket() http-localhost/127.0.0.1:8443-1, javax.net.ssl.SSLHandshakeException: sun.security.validator.ValidatorException: PKIX path building failed: sun.security.provider.certpath.SunCertPathBuilderException: unable to find valid certification path to requested target http-localhost/127.0.0.1:8443-1, called close() http-localhost/127.0.0.1:8443-1, called closeInternal(true)
The above error indicates a missing trusted certificate in the trusted Java store. Some other cases where, you already have the certificate but there is a problem with its validity, you may see the following error (“timestamp check failed“).
handling exception: javax.net.ssl.SSLHandshakeException: sun.security.validator.ValidatorException: PKIX path validation failed: java.security.cert.CertPathValidatorException: timestamp check failed.
We will be addressing the first scenario in which there is no certificate available (certificate_unknown).
Unable to Find Valid Certification Path to Requested Target: Possible Reason For The Error
If we look at the phase of the SSL handshake we’re in, we can see that we’ve already sent our client certificate and finishing up the handshake when we receive this error.
2015-02-04 21:59:33,002 INFO [stdout] (http-localhost/127.0.0.1:8443-2) - - *** ServerHelloDone
http-localhost/127.0.0.1:8443-2, WRITE: TLSv1 Handshake, length = 865
http-localhost/127.0.0.1:8443-1, READ: TLSv1 Handshake, length = 865
*** ServerHello, TLSv1
RandomCookie: GMT: 1406265764 bytes = { 30, 87, 196, 168, 159, 159, 7, 254, 62, 168, 199, 80, 108, 117, 48, 3, 113, 72, 1, 226, 31, 195, 238, 86, 88, 192, 96, 94 }
Session ID: {84, 210, 234, 164, 204, 121, 25, 56, 166, 145, 81, 180, 26, 103, 98, 72, 207, 54, 246, 139, 136, 17, 1, 140, 50, 131, 195, 18, 157, 80, 142, 4}
Cipher Suite: SSL_RSA_WITH_RC4_128_MD5
Compression Method: 0
Extension renegotiation_info, renegotiated_connection:
***
%% Created: [Session-9, SSL_RSA_WITH_RC4_128_MD5]
** SSL_RSA_WITH_RC4_128_MD5
*** Certificate chain
Version: V3
Subject: CN=************************************
Signature Algorithm: SHA1withRSA, OID = *********************
Key: Sun RSA public key, 2048 bits
.................................................
...................................................
***
SEND TLSv1 ALERT: fatal, description = certificate_unknown
WRITE: TLSv1 Alert, length = 2
READ: TLSv1 Alert, length = 2
called closeSocket()
RECV TLSv1 ALERT: fatal, certificate_unknown
called closeSocket()
handling exception: javax.net.ssl.SSLHandshakeException: Received fatal alert: certificate_unknown
handling exception: javax.net.ssl.SSLHandshakeException: sun.security.validator.ValidatorException: PKIX path building failed: sun.security.provider.certpath.SunCertPathBuilderException: unable to find valid certification path to requested target
The above error stack trace is actually helpful. It says that “unable to find valid certification path to requested target“. This means that the certificate the server certificate is not issued by certification authority, but a self signed or issued by a private CMS. If the certificate is issued by a trusted authority (VeriSign etc) the error will not happen.
Fix for PKIX path building failed Error:sun.security.provider.certpath.SunCertPathBuilderException
All you need to do to fix this error is to add the server certificate to your trusted Java key store. First You need to download the document from the server.
To download: access the URL of the service from any browser.You will get a certificate related warning message. Click on view certificate and then Install certificate. You can export the certificate from browser to some location in hard drive (In IE go to Tools->’Internet Options’ ->Content->Certificates).
Once you have the certificate in your hard drive you can import it to the Java trust store. To import the certificate to the trusted Java key store, you can use the java ‘keytool‘ tool.
Use keytool command as follows to import the certificate to JRE.
keytool -import -alias _alias_name_ -keystore ..\lib\security\cacerts -file _path_to_cer_file
It will ask for a password. By default the password is “changeit”. If the password is different you may not be able to import the certificate.
Note: You can also use the installcert java program from here.
Once completed restart/re-run your client application. You will be able to see successful SSL handshakes.
References:
- X.509 Public-key and attribute certificate frameworks
- Internet X.509 Public Key Infrastructure Certificate and CRL Profile RFC 2459
- Import the Certificate as a Trusted Certificate
Incoming search terms:
- pkix path building failed
- pkix validation failed
- PKIXPathBuildingFailed(Validation):sun security validator ValidatorException
- sun security validator ValidatorException: PKIX path building failed: sun security provider certpath SunCertPathBuilderException: unable to find valid certification path to requested target
- https://java globinch com/enterprise-java/security/pkix-path-building-failed-validation-sun-security-validatorexception/
- calm7fn
- javax net ssl SSLHandshakeException: sun security validator ValidatorException: PKIX path building failed: sun security provider certpath SunCertPathBuilderException: unable to find valid certification path to requested target
Is it possible to get this exact error and the certificate is in the truststore? Perhaps the service call is using an incorrect url or the path to the truststore is wrong in the application software? Also see in the ssl debug log adding certs log info. Where is it adding those certs too?
Thank you
When I downloaded the server cert from the browser, there were 3 certs in the file saved to disk. Do they need to be imported into the truststore as a chain for one alias name or 3 separate alias s
Hi,
Can u please explain how to overcome from have the certificate but there is a problem with its validity, we are seeing the following error (“timestamp check failed“)
javax.net.ssl.SSLHandshakeException: sun.security.validator.ValidatorException: PKIX path validation failed: java.security.cert.CertPathValidatorException: timestamp check failed.
please help on this
Some other cases where, you already have the certificate but there is a problem with its validity, you may see the following error (“timestamp check failed“).
Can you please send me the solution for the above scenario?
Thanks in advance